Event Types
Static Analysis D-Brain
Static Analysis uses the D-Brain to detect and prevent malicious files. The D-Brain is a prediction model that detects cyber threats including ransomware. Static analysis scans are performed on files.
Behavioral Analysis (Supported for Windows and MacOS)
Behavioral Analysis is for determining malicious intent in running processes and services.
Behavioral Analysis monitors and prevents on-execution malicious activities which also includes contextual script behavioral analysis.
Suspicious Script Execution
If one of the script processes (PowerShell, ActiveScript or MSHTA) is being created, and its parent process is in a global list of process names configured for “suspicious”.
Malicious PowerShell Execution
If a PowerShell command contains a string that is in a global list of commands configured for “malicious”.
Suspicious PowerShell Execution
If a PowerShell command contains a string that is in a global list of commands configured for “suspicious”.
Remediating the Events
The first step to remediating the Event is to investigate and determine if the file, process, or script is malicious or if it is deemed safe by the responsible Cybersecurity Team on your side.
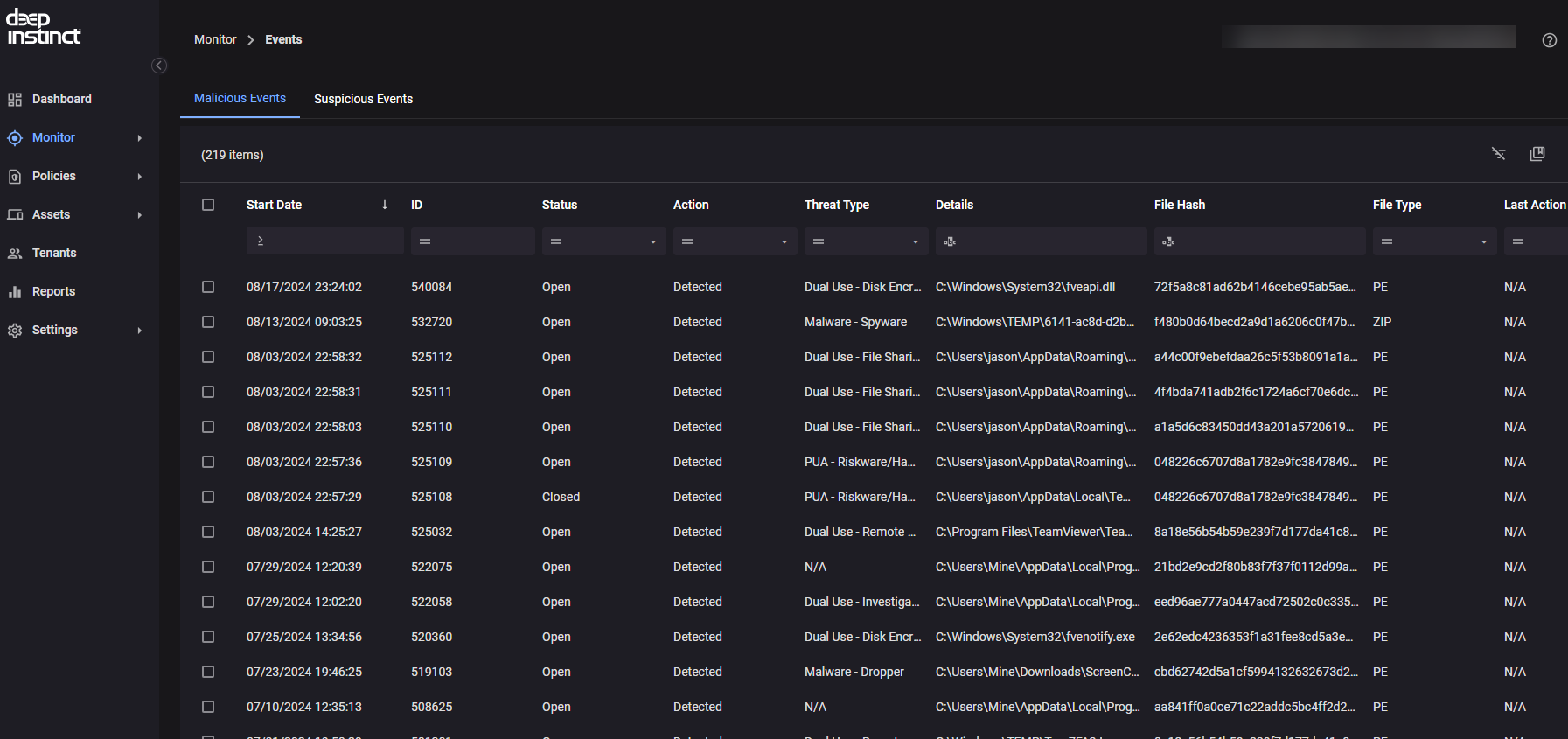
To begin the investigation, you can browse to Monitor -> Event Types in your Deep Instinct Console. Here you will see a list of all Events, the Event ID, Status, Action, Threat Type, and more. You can filter and search for specific entries for each column
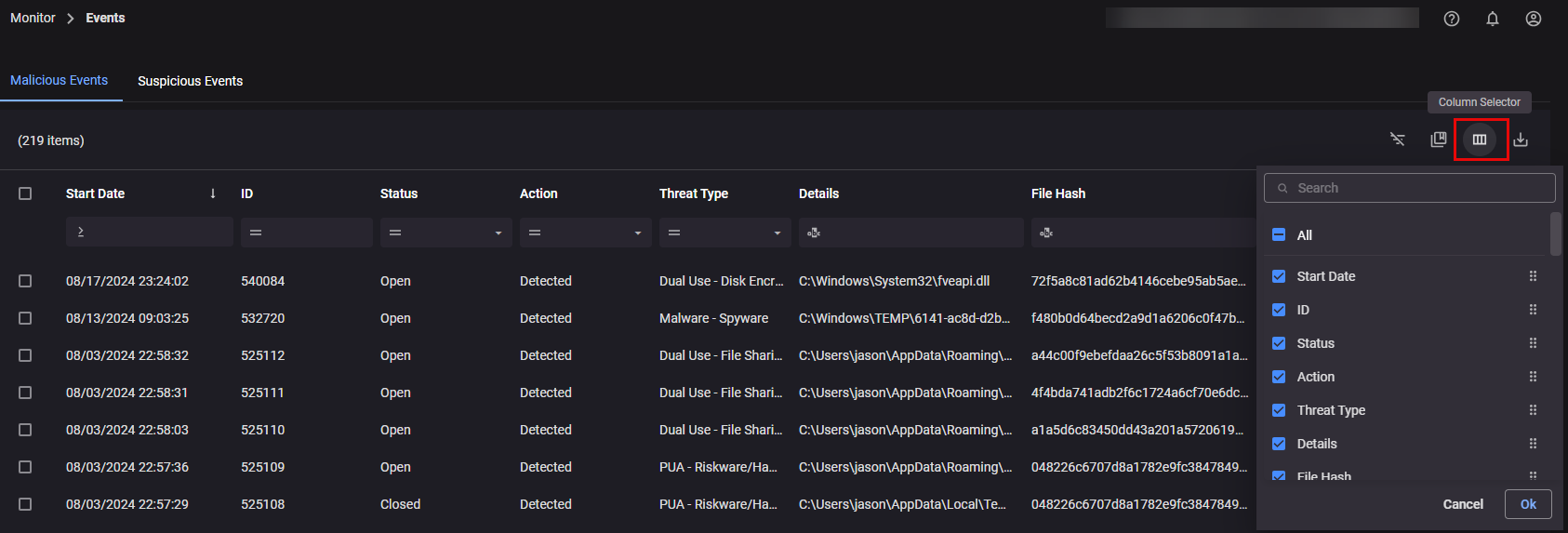
You can also customize the view of which columns are showing by selecting the “Column Selector” to the right:
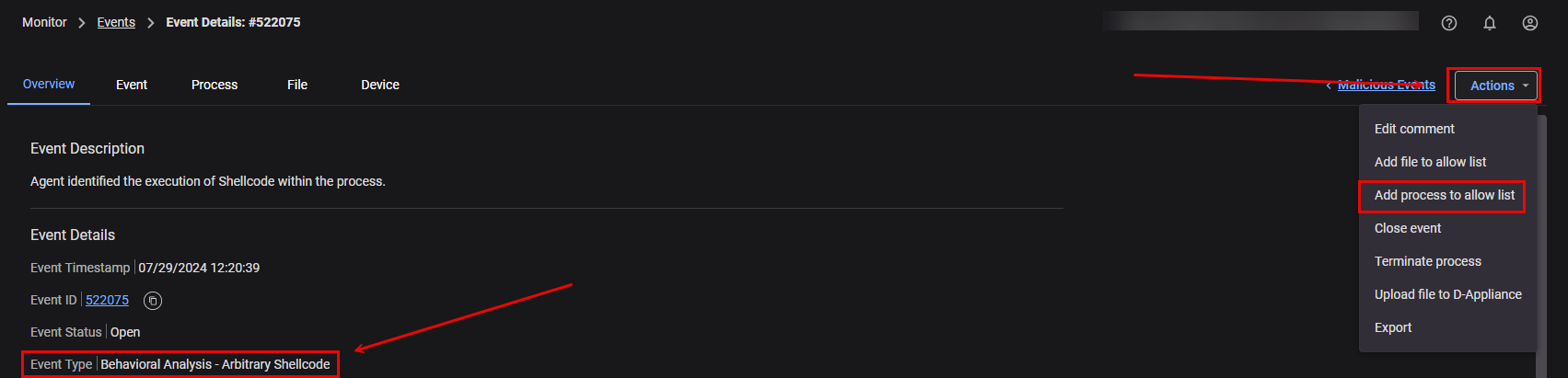
To view more details of the Event, you can left mouse click on the Event. Here you will see a more depth overview of the Event including the Event, the process that captured the Event, the file, and the Device the Event Occurred on:
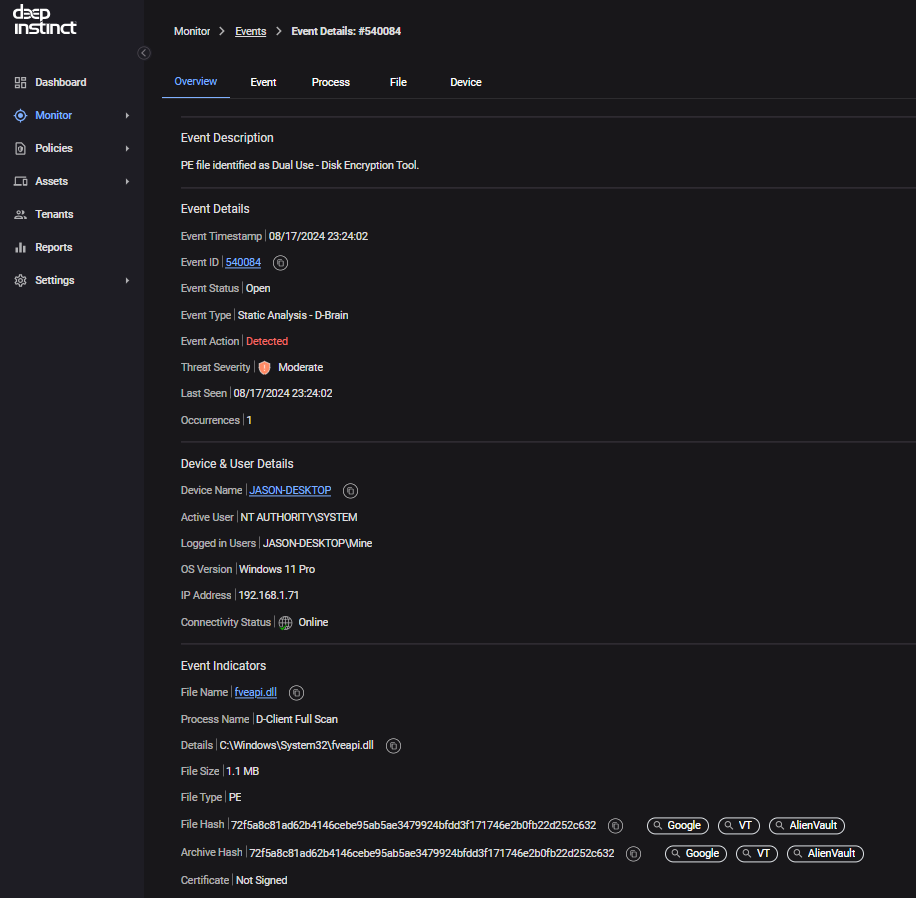
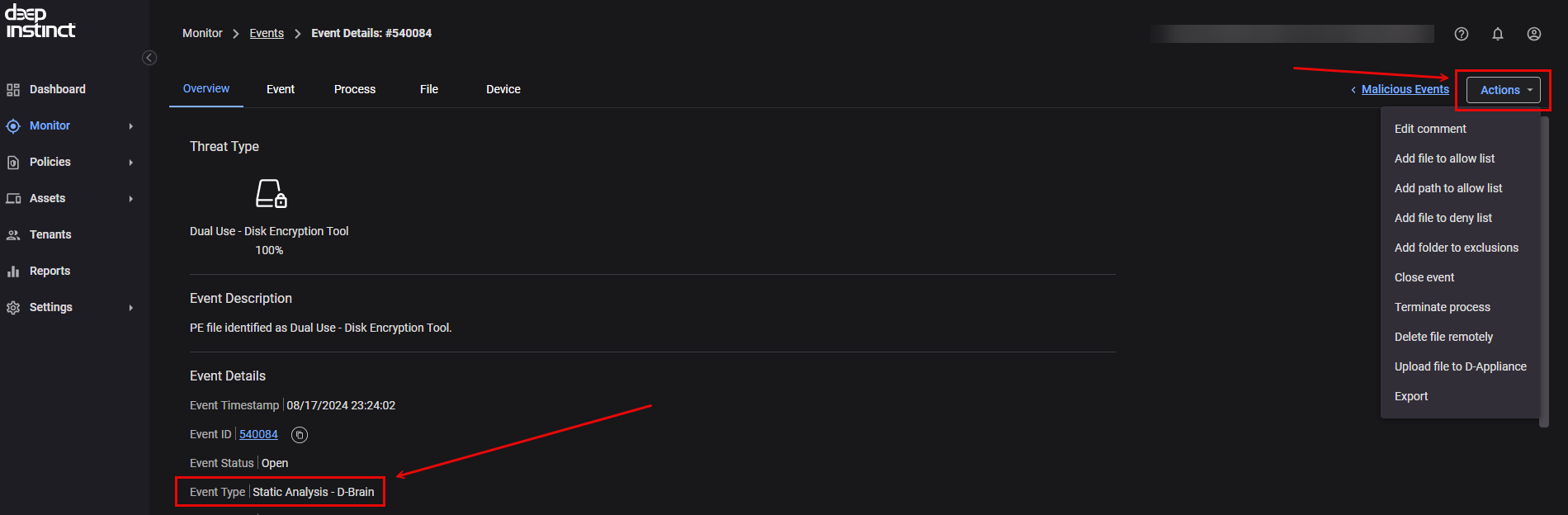
If after the investigation process by the responsible Cybersecurity Team on your end the Event is deemed to be safe, you can add it to the allow list as a file, a file path, the file hash, certificate, a process, or a script depending on the Event itself. Then apply the “Allow List” item to the correct Group Policy. To understand how to add it to the allow list, you can refer to the “Event Type”. If the Event Type is Static Analysis - D-Brain, it will need added as either a File with the File Hash, adding the file path to the allow list, or the Certificate. If it is determined to be malicious, adding the file hash to the deny list.
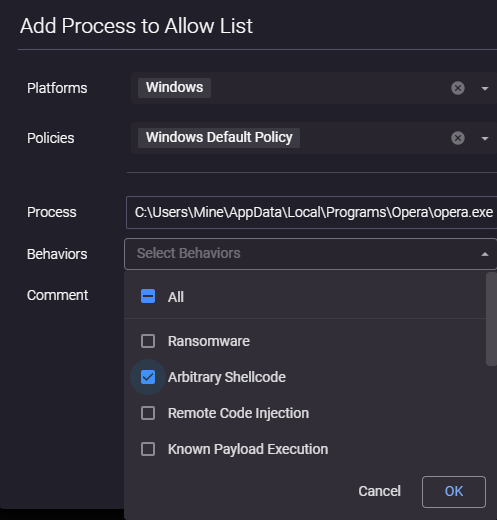
If the Event Type is Behavioral Analysis, it will need added to the allow list as a process while also specifying the correct subcategory of Behavioral Analysis. In the below example, it is Arbitrary Shellcode.
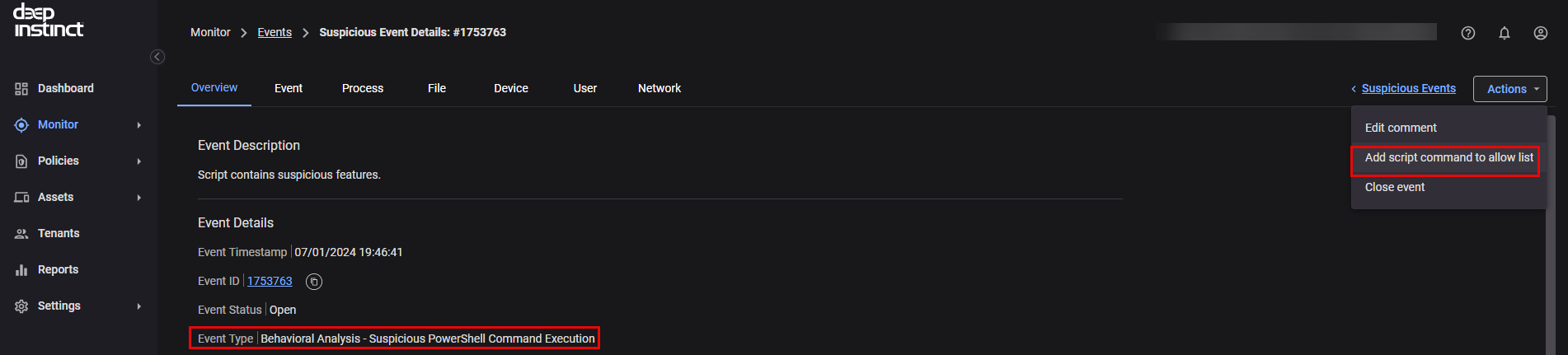
If the Event stems from a script execution, it can be added to the allow list as a script command
Files, Processes, and Scripts can also be added to the Allow List without an Event occurring first. You can browse to Policy -> Allow List and selecting the appropriate type. Behavioral Analysis is for adding the process to the allow list
When adding a file or process to the Allow List or Exclusion List without an Event, you can also choose to use wildcards in the path:
Process
Always end with: “\<file_name>.exe” or “*.exe” or “\*”
For example, for the following process:C:\Users\admin\Desktop\test4\user1\sub\test.exe
Process exclusion could be:
Example:
C:\Users\admin\Desktop\test4\user*\sub\test.exe
C:\Users\admin\Desktop\test4\user*\sub\*.exe
C:\Users\*\test4\user*\sub\*.exe
*\test4\user*\sub\*.exe
*\test4\user*\sub\*
File
Always end with:\*
File exclusion could be:
Example:
C:\Users\admin\Desktop\test4\*
C:\Users\admin\Desktop\test4\user*\*
C:\Users\admin\Desktop\test4\user1\sub\*
C:\Users\*\sub\*
*\test4\*
It is important to remember that a thorough investigation of the event with the responsible CyberSecurity Team on your end is highly recommended before adding anything to the Allow List to ensure that your devices have the best protection. If you have any questions about a specific event, please do not hesitate to contact us